Operator
Operators run the software that keeps decentralized networks alive. They include node operators or validators that run consensus and network-specific binaries, sign messages for bridging and oracles, or strategy operators such as risk managers and AI agents that execute DeFi strategies on behalf of a network.
Within Symbiotic, operators can receive stake from different vaults and route it to the same set of nodes for a given network. The protocol maintains a registry of operators and records their activity so networks and curators can make informed choices. The registry covers which networks an operator has opted into, which vaults are connected and how much restaked collateral came from them, and a history of slashes and other on chain interactions.
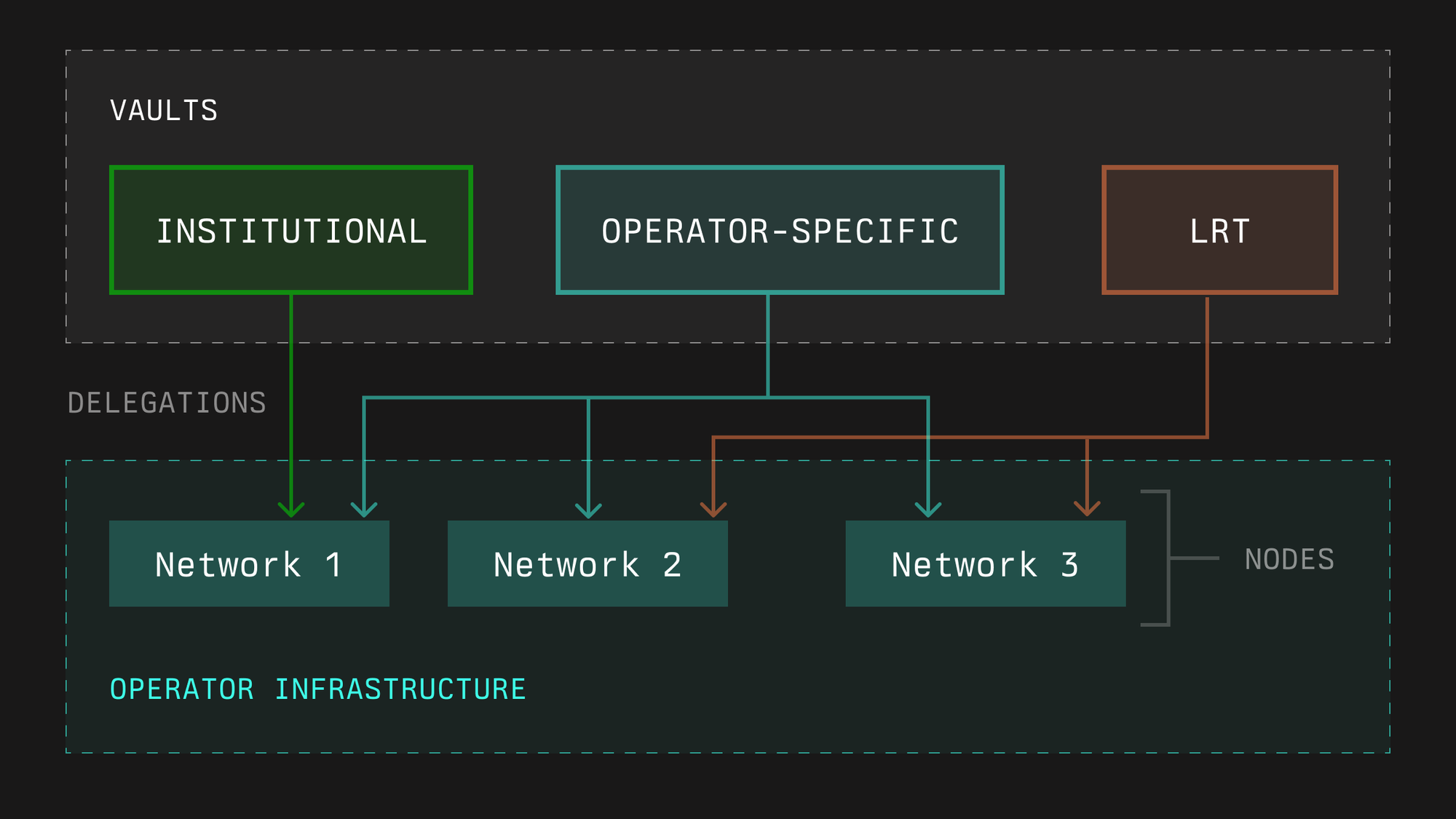
This setup lets operators aggregate stake from many sources, including institutional vaults, operator specific vaults, or LRTs with different risk profiles, without spinning up separate infrastructure for each one. A single node stack per network can secure multiple partners, as long as all parties have opted in.
In Symbiotic, an operator is either an externally owned account or a contract registered in the OperatorRegistry.
Operator onboarding
At a high level, onboarding an operator involves three steps.
- Register the operator entity in the operator registry so it can be referenced by vaults and networks: Call
OperatorRegistry.registerOperator()inOperatorRegistry. - Opt into the networks the operator wants to serve. Each network decides whether to include the operator in its active set based on criteria such as performance history, reputation, stake, and reliability. This is achieved by calling the
optIn()method inOperatorNetworkOptInService. - Opt into the vaults that may allocate stake to that operator. This is achieved by calling the
optIn()method inOperatorVaultOptInService. Curators then configure limits or shares so the Delegator can route stake to the operator within each network’s bounds. The address that holdsOPERATOR_NETWORK_SHARES_SET_ROLEorOPERATOR_NETWORK_LIMIT_SET_ROLEfor the vault assigns stake to the operator by calling either:D.setOperatorNetworkShares(...), orD.setOperatorNetworkLimit(...)depending on the Delegator type used by the vault.
Stake becomes eligible for slashing only when the operator has opted into both the network and the vault at the time stake is captured for an epoch.
Working with Vaults and Networks
Vaults
Vaults are where stake lives. Curators decide which operators are admissible for a vault and how much stake each one can receive. They set per operator limits or shares and may adjust them as conditions change. The Delegator module uses these settings, together with opt ins, to determine how much effective stake each operator has per network.
Networks
Networks are where operators perform work. An operator opts into a network in order to validate it or to provide a defined service. Based on its own criteria, each network independently decides whether to include the operator in the active operator set. The network’s software produces work, emits messages or commitments to be attested, and participates in epochs. Here the network defines voting power rules and thresholds, message formats, participation and liveness requirements, dispute inputs, and how it integrates with the Relay if it needs cross chain verification.
Aggregation
For a single network, an operator can combine stake from multiple vaults into one node stack as long as:
- the operator has opted into that network
- the operator has opted into those vaults
- curators have allocated stake to the operator within each network limit
This allows operators to build one hardened infrastructure per network and receive stake from many partners without fragmenting their setup.
Subnetworks and Keys
Some networks split responsibilities into subnetworks. Limits, stake capture, and any penalties apply per subnetwork. Operators should plan key management and operations with that boundary in mind, for example by running distinct keys or processes per subnetwork where needed.
Relay integration
All of the above can be implemented with custom network logic, but wiring cross chain verification, aggregation, and stake capture from scratch is complex. Symbiotic provides the Relay SDK so networks and operators can plug into a common framework instead.
If a network uses the Relay SDK:
- The Relay uses the operator registry and voting power from Symbiotic to build the operator set for that network.
- Operators can run a small Relay sidecar that helps collect signatures, aggregate them, and submit commitments so verification remains efficient across EVM chains.
- The same operator set and stake that secure the network can be reused to attest on multiple chains, reducing costs and integration effort while keeping the network’s governance and rules unchanged.
From the operator perspective, Relay integration mainly means running an additional, lightweight process that works alongside their existing nodes and keys, rather than rewriting their own cross chain logic.
Penalties and Slashing
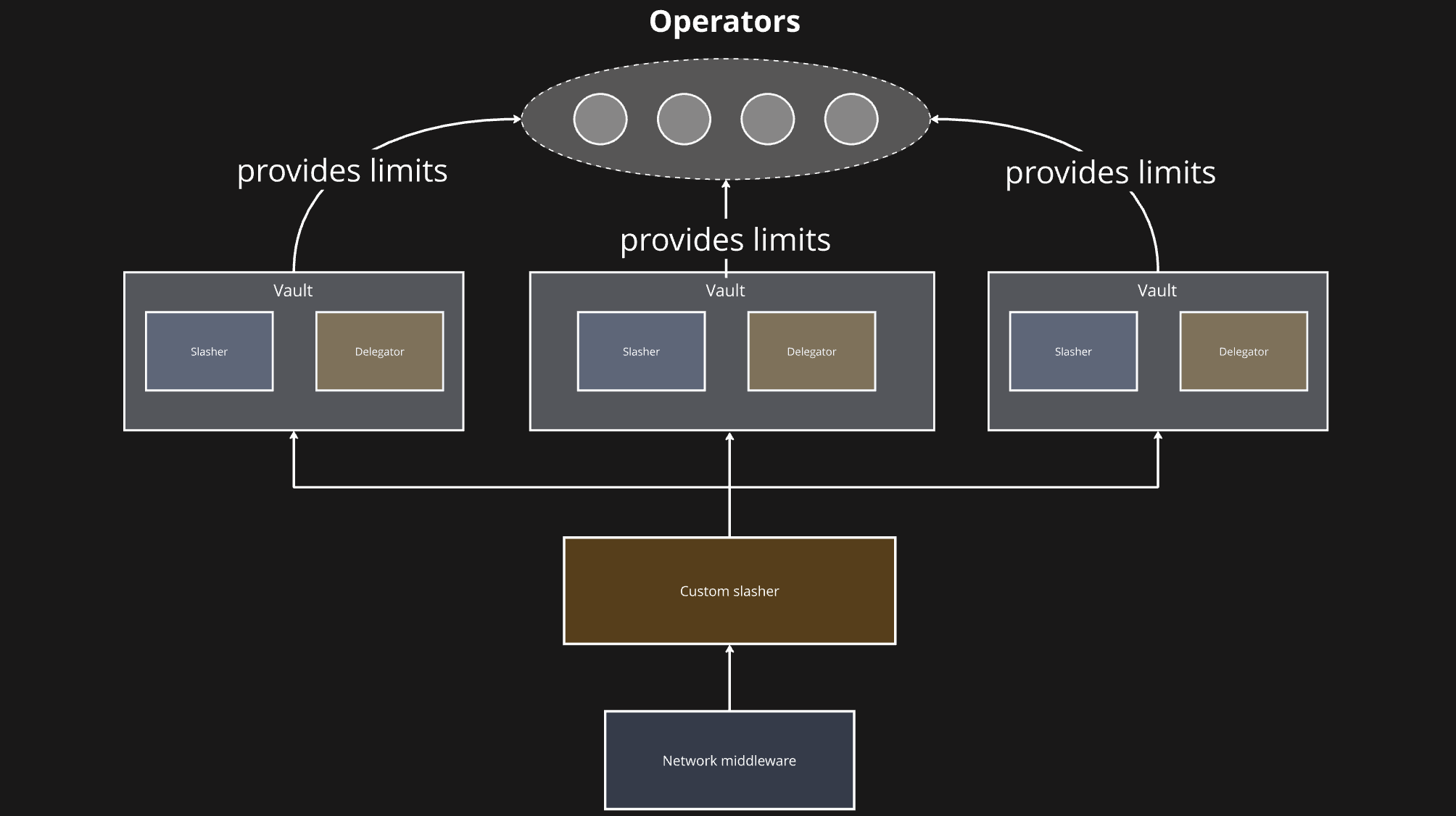
Once an operator has opted into a vault and a network, and stake has been captured for an epoch, that stake becomes subject to slashing according to the network rules and the vault configuration.
If an operator fails to perform services according to those rules, the network middleware can raise a slashing request against the operator’s stake. On Ethereum style systems this includes faults such as double signing or other consensus violations. The vault’s Slasher module validates slashing requests and, if they are correct and within the defined guarantees, applies penalties to the operator’s stake and invokes the vault’s Burner to decide what happens to the penalized collateral.
Some setups allow immediate execution of valid slashes, while others introduce a short veto or review window, depending on the Slasher type chosen by the curator and the network.
Rewards
Operators need to be compensated for the services they provide and the risk they take. Networks pay operators from the value they generate, for example protocol fees, payments from external clients who use their services, or token inflation allocated to security and operations.
See Learn: Rewards to learn more about reward distribution mechanisms.
